What is a software vulnerability?
A software vulnerability is a weakness or gap in security checks within a software component that can allow an attacker to perform unauthorized actions. Software vulnerabilities in this context relate to how the software has been built, as opposed to how it has been configured and implemented. End users of the software are in control of how the software is configured to protect against cyber-attack, but have no control over how the software is built.
How are software vulnerabilities measured?
The Common Vulnerability Scoring System (CVSS) is an open standard for assessing the severity of software vulnerabilities. It considers factors such as the ease with which a software vulnerability can be exploited, and the impact of any exploits. It is a numerical scale from 0 – 10 with 10 being the most severe. CVSS defines vulnerabilities with a score of 9 – 10 as ‘critical’. CVSS is owned and managed by a non-profit organization called First.Org, Inc (https://www.first.org/cvss/)
How often are vulnerabilities found?
Critical vulnerabilities are rare. They are, however, very visible since they are often published in news and social media channels. Most vulnerabilities are not critical in risk or impact and are addressed as part of our ongoing software quality and release processes.
How do Synectics monitor for software vulnerabilities?
Synectics software products are built using a combination of proprietary and third-party components. When we build new releases of our software, we check the components against a regularly updated list of known vulnerabilities. We also monitor various digital channels used for reporting vulnerabilities.
We then analyse the severity and impact of the vulnerability when deployed within our software solutions. This is an important step: a critical vulnerability identified in a third-party component may not be critical in the context of a Synergy deployment.
Why use third-party components?
We want our customers to have ‘best of breed’ software solutions. Using third party components allows us to leverage expertise across multiple areas (e.g. logging) and enables us to focus on our core strengths in security, surveillance and workforce management solutions.
Using third-party components is common practice in software development.
What happens when a critical vulnerability is confirmed?
We identify mitigation steps to reduce the vulnerability and also work on a ‘hot fix’. Just as important is the external communication so you are informed of how the vulnerability can be managed.
What is a ‘hot fix’?
If the vulnerability is assessed as being critical for our customers it may need to be addressed outside of our product release cycles. A ‘hot fix’ is a time-sensitive non-functional release of our software. Depending on the software platform it will be automatically applied or made available as a downloadable installer. For example, our mobile solutions will have the hot fix automatically pushed out whilst Synergy will require a system administrator or integrator to install an update.
Are hot fixes compatible with all versions of Synergy?
We endeavour to release hot fixes that are backward compatible with previous versions of Synergy 3. Where this is not possible, we will indicate this in our hot fix documentation and comms regarding the vulnerability.
How do Synectics communicate critical vulnerabilities?
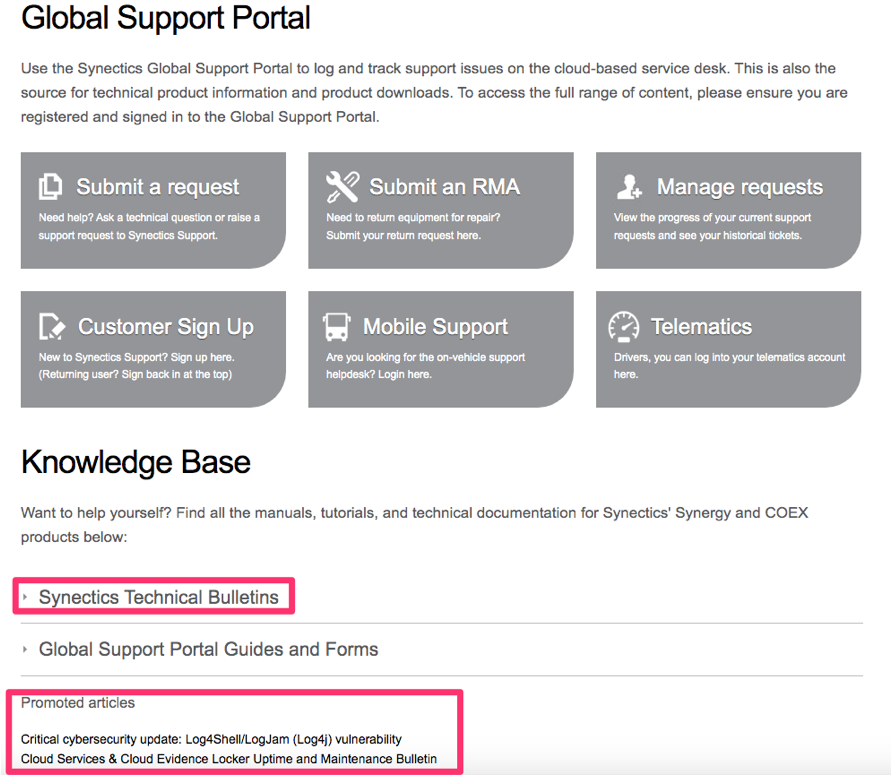
Our Knowledge Base on the Global Support Portal contains Tech Bulletins to communicate critical vulnerabilities. We also promote important content so that is easier for you to find without logging into the Global Support Portal. Where appropriate we send out emails to advise on critical issues and next steps.
You can find the Technical Bulletins and promoted articles on the home page of the Global Support Portal.